Tracing Crypto Assets
For most people, crypto fraud does not begin as a technical problem. It begins as a shock.
Someone checks a wallet and sees funds gone. A transfer they do not recognize has already been confirmed. A fake investment platform stops responding. A scammer who sounded convincing a day earlier suddenly disappears. In that moment, most victims are left with the same questions. Where did the money go? Can it still be traced? Is there anything practical to do next?
This is where crypto tracing becomes important.
Tracing crypto assets is one of the first serious steps in understanding what happened after a theft, scam, wallet compromise, or suspicious transfer. It helps turn panic into facts. Instead of guessing, tracing looks directly at the movement of funds on the blockchain and begins building a clear picture of where those assets went, how they moved, and whether they passed through exchanges, services, or other identifiable points along the way.
At Crypto Recovery Authority, we believe people need honest, well-explained guidance, especially when they are dealing with loss and uncertainty. This guide is written to explain crypto tracing in a practical way, not in vague industry language. It will show what tracing actually is, what it can reveal, where its limits are, and how our team helps clients make sense of complex blockchain movement with evidence-based analysis and reporting.

What Crypto Tracing Really Means
Crypto tracing is the process of following digital assets as they move across the blockchain.
That may sound simple, but in practice it involves much more than looking up a wallet address on a public explorer. Real tracing means examining a chain of transactions and understanding the story behind them. It means identifying where the assets started, where they went next, how they were split, whether they were swapped into another token, whether they moved onto another chain, and whether they eventually reached a service like an exchange or payment platform.
Every blockchain transaction leaves a record. On public chains, those records are visible. Wallet addresses, incoming transfers, outgoing transfers, token movements, timestamps, and contract interactions all leave data behind. What tracing does is interpret that data carefully.
For example, when someone loses funds in a scam, the first receiving wallet is rarely the end of the story. The scammer may move the assets again within minutes. They may split them across several wallets. They may convert them into another token. They may bridge them to a different blockchain. They may send them into an exchange deposit address. To a victim, this can look like the funds have vanished. In reality, the path often still exists, but it needs to be reconstructed.
That is why crypto tracing is investigative work, not guesswork. It is about following the movement of value from one transaction to the next and understanding what each step is likely doing.
Done properly, tracing helps answer practical questions such as:
- What was the first wallet that received the funds?
- How quickly were the funds moved?
- Were they split into several paths?
- Were they swapped or bridged?
- Did they interact with a service or exchange?
- Does the wallet activity look like a larger scam pattern?
This is what makes tracing useful. It does not rely on assumptions. It relies on transaction evidence.
How Blockchain Transparency Helps Investigations
A lot of people still believe cryptocurrency is impossible to track. That idea is one of the biggest misunderstandings in this space.
Most major blockchains are not invisible. They are public. What they do not always show is the real-world identity behind a wallet. That is an important difference. Crypto is often pseudonymous, not automatically anonymous.
When someone sends or receives funds on a public blockchain, that movement becomes part of a permanent record. Investigators can review the wallet's transaction history, identify connected addresses, look at timing patterns, review token transfers, and track interactions with smart contracts or bridges. Over time, these movements can reveal meaningful clues.
This is especially important in fraud cases because scammers tend to rely on complexity more than true invisibility. They move funds quickly because they want victims to feel lost. They add extra transfers because they want the path to look confusing. They may use multiple wallets, decentralized swaps, or chain bridges because they assume the average person will stop looking after the first few hops.
But complex movement is still movement. It still creates a trail.
Blockchain transparency helps investigators piece together that trail by showing:
- Exact wallet-to-wallet transfers
- Movement times and sequence
- Token swaps
- Smart contract interactions
- Repeated routing patterns
- Wallet consolidation behavior
- Exchange deposit style activity in some cases
This does not mean every case is easy. It does mean that public blockchain data can be far more informative than victims initially realize.
What Can Be Traced
The practical value of crypto tracing comes from understanding what investigators can actually follow on-chain.
In many cases, direct transfers between wallets can be traced clearly. If funds moved from a victim's wallet into a receiving address, that first hop is usually visible. If the scammer then moved those funds again, that next step can often be followed as well. If the funds were split into smaller amounts and routed into several wallets, that pattern may also be visible.
Token movement can often be traced too. If stolen ETH is swapped into stablecoins, or if USDT is moved and then bridged, that activity may leave a clear sequence of transactions. The same is true for many contract interactions. A scammer might believe a token swap hides the movement, but in practice, swaps often add more clues rather than fewer.
Investigators may also be able to identify patterns such as:
- Funds being split to reduce attention
- Multiple victim deposits landing in the same wallet cluster
- Assets being consolidated again after several transfers
- Interaction with known decentralized protocols
- Movement into wallets that appear to serve exchange deposits or service intake points
- Repeated transaction structures that suggest a routine scam operation
What tracing often reveals is not just where the money went, but how the operator behind the movement behaves. That behavior matters. In some cases, it helps show whether the activity was random, amateur, or part of a broader organized fraud pattern.
Still, it is important to be realistic. Tracing does not always end with a neat answer or a named individual. But even when identity is not immediately visible, the transaction path itself can be highly valuable.
If you have lost crypto and want to understand where it went, our team can help trace the movement and build a clear picture of the fund flow.
Start Your Free Case EvaluationWhat Makes Crypto Tracing Difficult
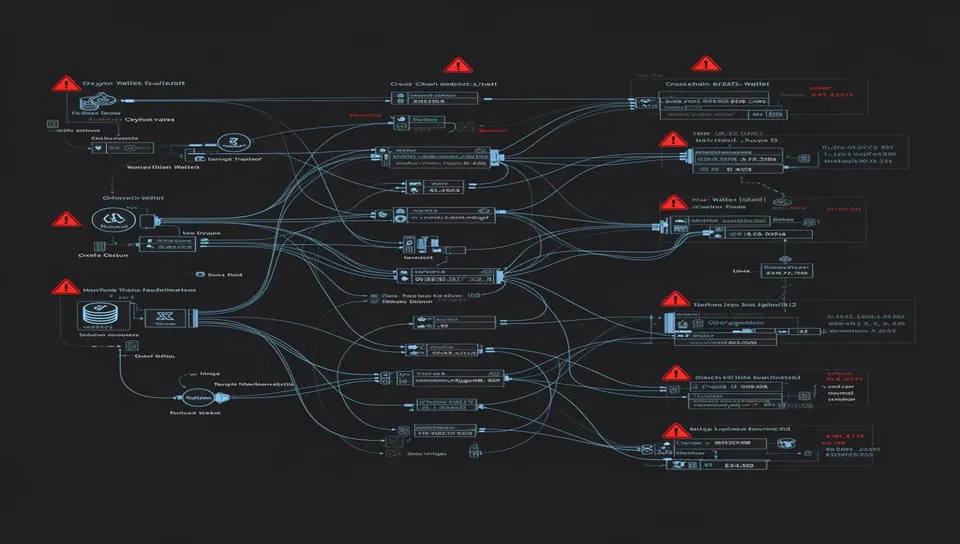
Crypto tracing can be powerful, but it is not effortless. Some cases are straightforward. Others are much more complex.
One challenge is speed. Scammers often move funds immediately after receiving them. They may create long chains of transactions in a short period to make the movement look overwhelming.
Another challenge is wallet layering. Instead of sending stolen assets directly to one destination, scammers may route funds through many intermediate wallets. This creates noise, but it does not necessarily destroy the trail.
Cross-chain activity adds another layer of difficulty. A scammer may move assets from one chain to another using bridges or swap mechanisms. When that happens, investigators need to follow the movement across ecosystems rather than treating the first blockchain as the end of the story.
Privacy-focused tools can also complicate tracing. Certain services and assets are designed to reduce visibility or make transaction analysis harder. Mixers, obfuscation methods, and privacy-centric environments can limit what is visible on-chain.
Decentralized protocols can also create investigative challenges. When assets move through non-custodial systems, there may be fewer obvious service records than there would be with a centralized platform.
But here is the important point: difficulty is not the same as impossibility.
A complex trail may take more effort to map. A privacy layer may reduce clarity. A chain bridge may extend the investigation. Yet these obstacles do not automatically erase the value of tracing. In many cases, the surrounding transaction context still reveals useful patterns, timing, and strategic touchpoints.
Why Victims Need More Than a Block Explorer
A blockchain explorer is useful, but it is only a starting point.
Many victims open a public explorer, paste in a wallet address or transaction hash, and quickly realize they are staring at a wall of numbers, addresses, and contract calls that do not answer the question they actually care about. Seeing transaction data is not the same as understanding transaction data.
A block explorer can show that a transfer happened. It does not necessarily explain:
- Why that transfer matters
- Whether the receiving wallet is one of many linked addresses
- Whether the funds were routed in a pattern typical of scam activity
- Whether a later transfer appears to be an exchange deposit
- Whether the token swap was likely intended to obscure the trail
- Whether there are signs of a larger fraud network behind the case
That gap between visible data and meaningful interpretation is where professional tracing adds value.
Tracing is not just about collecting addresses. It is about organizing movement into a coherent case picture. That includes identifying what matters, ignoring what does not, and documenting the path in a way that is useful for the victim and, where relevant, for legal or reporting purposes.
This is especially important because victims are often under emotional pressure. They need clarity, not more confusion. They need facts, not speculation.
How Crypto Tracing Is Actually Done
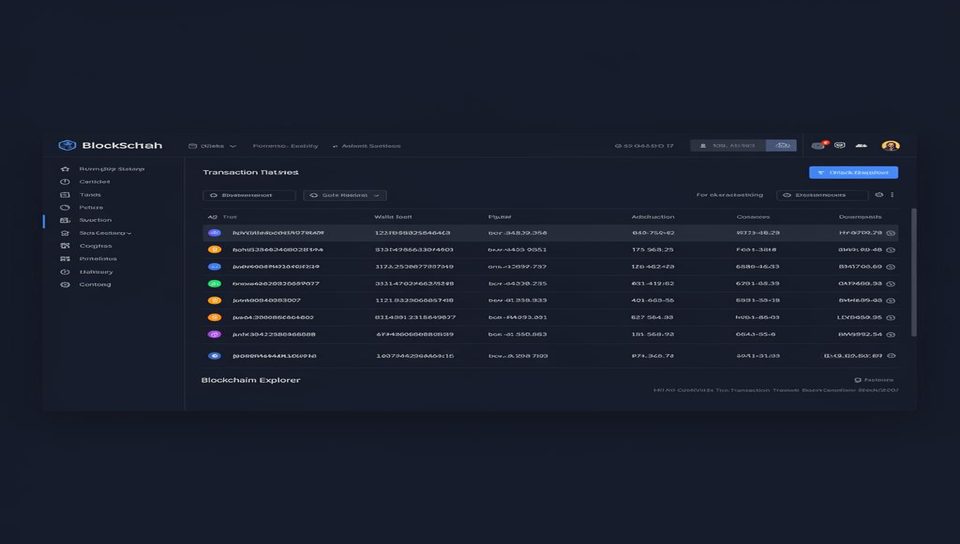
A real tracing review begins with the available evidence.
That may include wallet addresses, transaction hashes, screenshots, exchange records, emails, scam messages, website details, or any other material tied to the loss. The first goal is to make sure the core transaction path is identified accurately from the start.
From there, the tracing work usually begins with the first receiving wallet. Investigators look at when the funds arrived, how much was received, whether multiple victim deposits appear in the same wallet, and how quickly the funds were moved again. That first layer can already reveal whether the wallet behaves like a holding point, a pass-through address, or a collection wallet.
Next comes transaction path mapping. This is where the analysis moves from one wallet to the next, following secondary and tertiary transfers to see whether the funds were split, merged, swapped, or bridged. In some cases the path remains simple. In others it expands into a broader cluster of related movements.
As the path develops, investigators review behavior patterns. Are similar amounts moving in repeated cycles? Are funds regularly routed through the same types of services? Are there indications of automated laundering behavior? Are the wallets interacting with known decentralized protocols or identifiable service structures?
One of the most important parts of tracing is identifying service touchpoints. If funds eventually move into a centralized exchange environment or another custodial service, that can become a key finding. Even when tracing does not immediately produce a real-world identity, identifying the right service endpoint can still matter strategically.
Finally, the findings need to be documented properly. A good tracing result is not just an internal conclusion. It is an organized explanation of what happened, supported by transaction evidence and presented in a clear way.
That is the difference between casual wallet checking and actual tracing work.

When Tracing Creates Real Value
Some people hear the word "recovery" and immediately assume the only useful outcome is getting every asset back. In reality, tracing creates value much earlier than that.
The first value is clarity. Victims often come into a case with incomplete or misleading information. They may think the funds are gone forever, or they may have been told by scammers that the assets are "locked," "staked," or "in processing." Tracing cuts through those stories by showing what the blockchain actually says.
The second value is factual direction. Once the fund movement is understood, the victim is in a much stronger position to decide what to do next. That may involve formal reporting, preserving evidence, reviewing platform touchpoints, or assessing whether the case shows any realistic service-linked path worth escalating.
The third value is documentation. A properly traced path can support case files, legal discussions, internal records, or investigative reporting. Without organized tracing, the victim is often left with scattered screenshots and confusion.
The fourth value is emotional. That may sound unusual, but it matters. People who have been scammed often feel helpless because they do not know what happened. Evidence-based tracing gives them something solid to stand on.
Even when tracing does not produce an immediate recovery route, it can still replace uncertainty with facts. That alone is meaningful.
Our tracing work turns blockchain complexity into structured, evidence-based findings. If you need clarity about where your crypto went, we can help.
Request a Free Case EvaluationOur Crypto Tracing Services
Once the basics of tracing are clear, the next question is how professional support actually works in practice.
At Crypto Recovery Authority, our role is to turn confusing blockchain movement into structured, evidence-based intelligence. We do not rely on vague promises or generic wallet lookups. We focus on careful analysis, practical findings, and clear reporting.
Below is how our tracing services are built.

Transaction Tracing and Fund Flow Analysis
This is the core of our work.
We follow stolen or disputed funds across wallet paths and build a clear record of how those assets moved. That includes first-hop transfers, secondary movement, splitting behavior, consolidation patterns, token movement, and routing across multiple addresses.
In many cases, victims only know the first transaction. Our job is to take that starting point and reconstruct the broader movement path. That reconstruction matters because it often reveals whether the scammer used a simple pass-through wallet, a collection wallet, a chain of temporary addresses, or a structured laundering route.
Rather than leaving clients with isolated screenshots, we help build a transaction story that makes sense from start to finish.
Wallet Intelligence and Behavioral Analysis
Wallet addresses do not speak, but their behavior does.
Our wallet analysis work looks beyond single transfers to understand how an address or cluster of addresses behaves over time. We examine patterns such as repeated routing, timing similarities, shared movement structures, likely collection behavior, and other signs that can suggest scam activity or linked operational routines.
This kind of review can help show whether a case appears isolated or part of a broader network. It can also help identify whether multiple victim deposits appear to be flowing into the same ecosystem of wallets.
Behavior matters because fraud is often patterned. The wallets involved tend to leave habits behind.
Exchange and Service Identification
One of the most important tracing outcomes is identifying where funds may have reached a service or exchange.
When stolen assets move into a centralized platform environment, the case may begin to involve a more practical touchpoint. That does not guarantee an outcome, but it can be strategically important. Identifying those service-linked paths often helps clients understand whether there is a meaningful next step beyond simply watching wallets move.
Our work in this area focuses on recognizing service-style address behavior, deposit path indicators, and other signs that funds may have entered a custodial or structured platform setting.
This is often where tracing becomes especially important from a case strategy perspective.
Cross-Chain Tracing
Modern scam cases rarely stay on one blockchain.
Funds may be bridged, swapped, wrapped, or converted as they move across ecosystems. If tracing stops at the first chain boundary, the picture is often incomplete. That is why cross-chain review matters.
At Crypto Recovery Authority, we examine chain transitions carefully to understand how value moved beyond the first visible network. This helps create a more complete map of the asset path and reduces the chance of treating a bridge event as the end of the trail when it is really just a midpoint.
Cross-chain analysis is particularly important in more advanced fraud cases because scammers increasingly rely on speed and ecosystem complexity to discourage victims from following the movement further.
Forensic Reporting
Tracing is only useful if the findings can be explained clearly.
Our forensic reporting is designed to turn transaction complexity into something a client can actually understand and use. That includes organizing fund movement chronologically, identifying key addresses, highlighting service touchpoints, and presenting the findings in a way that supports practical decision-making.
A well-structured report helps separate confirmed findings from assumptions. It provides clarity around what was observed on-chain and why those observations matter.
This kind of reporting can be valuable not just for the client, but also for supporting broader case records where needed.
Case Review and Strategic Guidance
Clients do not just need traced transactions. They need help understanding what those results mean.
That is why our service also includes realistic case review and guidance. We help clients understand the significance of the traced path, the strength of the findings, whether meaningful service touchpoints appear to exist, and what practical next steps may be worth considering.
Just as importantly, we believe in honest communication. We do not use inflated claims or guaranteed language. Crypto tracing should be handled seriously, and clients deserve realism.
Our focus is on clarity, evidence, and direction.
Common Situations We Help With
Crypto tracing is relevant across many kinds of cases.
Fake investment platforms are one of the most common. A victim is persuaded to deposit funds into what appears to be a legitimate trading or wealth platform, only to discover later that balances were manipulated and withdrawals were never real.
Phishing attacks are another major category. These cases often involve stolen credentials, malicious links, fake support interactions, or deceptive wallet approval requests that lead to unauthorized transfers.
Wallet compromise cases can happen through drainer tools, malicious smart contracts, device compromise, or social engineering. In these situations, tracing often begins with the first unauthorized outflow and expands from there.
Rug pulls and project-related fraud can also require tracing, especially where token ecosystems, treasury wallets, and suspicious fund movement patterns are involved.
Then there are trust-based scams, including relationship-driven fraud and prolonged manipulation, where the victim willingly sent funds under false pretenses. These are often emotionally difficult cases, but the blockchain still tells an important story.
Why Clients Choose Crypto Recovery Authority
People come to Crypto Recovery Authority because they want a serious, detail-oriented approach.
They want more than a generic explanation of blockchain basics. They want careful tracing, clear communication, realistic expectations, and reporting built on evidence rather than speculation.
Our approach is designed around those needs. We take the time to examine the movement properly. We explain findings in a way clients can understand. We stay practical. And we treat every case like it matters, because for the person affected, it does.
Trust is especially important in this field. People who have already been scammed should not have to deal with empty promises all over again. Our work is built to provide the opposite: clarity, professionalism, and honest support.
Conclusion
Tracing crypto assets is often the first real step toward understanding a crypto loss.
It helps replace confusion with evidence. It shows how funds moved, where the trail leads, whether meaningful touchpoints exist, and what the case actually looks like on-chain. That kind of clarity matters, especially when a victim is trying to decide what to do next.
Crypto tracing is not magic, and it should never be sold that way. But when it is done properly, it can provide something extremely valuable: a factual understanding of what happened and a stronger foundation for any next step that follows.
At Crypto Recovery Authority, our goal is to provide exactly that. Careful tracing. Clear reporting. Honest guidance. Practical support.
If you need help understanding where your crypto went, start your case review with Crypto Recovery Authority and take the first evidence-based step toward clarity.
Need help understanding where your crypto went? Crypto Recovery Authority provides professional tracing support that turns complex blockchain movement into clear, evidence-based findings.
Start Your Case EvaluationRelated Resources
Can Stolen Crypto Be Traced?
How stolen crypto is traced and what blockchain analysis reveals.
Blockchain Tracing Services
Professional blockchain tracing and investigation support.
What Evidence Helps a Crypto Tracing Case
What to gather and preserve to strengthen your case.
What to Do in the First 24 Hours After a Crypto Scam
Critical first steps after discovering a crypto loss.