When cryptocurrency is stolen, one of the most common questions is whether the funds can be traced. The short answer is: often, yes. But what does tracing actually look like in practice? This guide walks through the real investigative process that professionals follow — from the first transaction to the final evidence package.
This is not a basic overview of whether crypto can be traced. That is covered separately. This guide is about the sequence — the actual steps investigators take, in order, when they are hired to trace stolen digital assets.
Step 1: Verify the Originating Transaction and Wallet Path
Every tracing engagement begins with the same question: what was the originating transaction? This means identifying the exact transaction hash where the funds left the victim's control — whether that was a direct transfer, a phishing-triggered approval, a wallet drain, or a deposit into a fraudulent platform.
Getting this right is essential. The wrong starting point means every subsequent step builds on incorrect assumptions. Investigators verify the transaction against the victim's records, wallet history, and timeline to ensure the trace begins at the correct moment.
Step 2: Identify Receiving Wallets and Transaction Clusters
Once the originating transaction is confirmed, investigators examine the receiving wallet. In most cases, this is not a single isolated address. It is part of a cluster — a group of wallets that appear to be controlled by the same entity based on their transaction patterns.
Cluster analysis is one of the core techniques in blockchain investigation. By examining how wallets interact with each other — shared inputs, common funding sources, timing patterns — investigators can build a picture of the entity behind the addresses, even without knowing their identity directly.
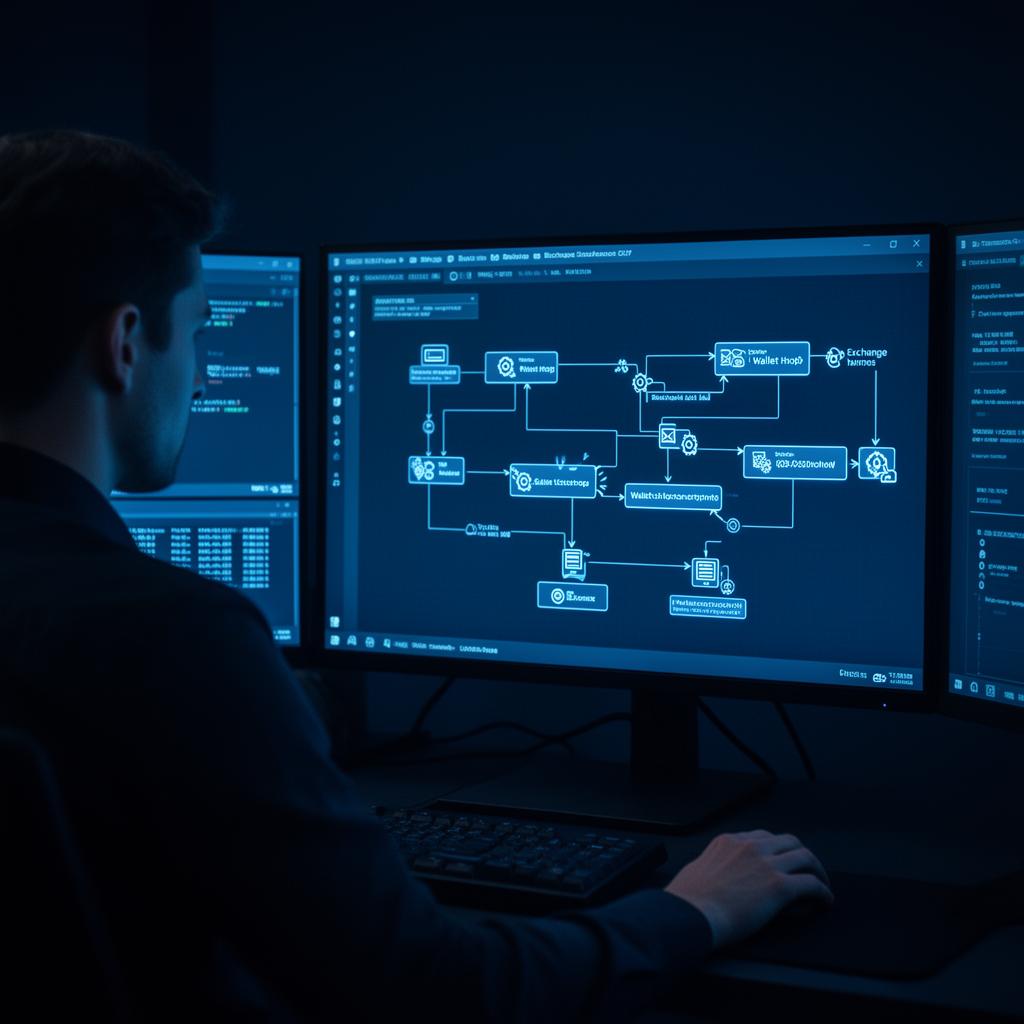
Step 3: Map Movement Across Chains, Services, or Exchanges
Stolen funds rarely stay in one place. Investigators follow the movement across multiple hops, tracking the assets as they are split, consolidated, swapped, or bridged across different blockchain networks.
- On-chain swaps between tokens using decentralised exchanges
- Cross-chain bridge transfers from one blockchain to another
- Deposits into centralised exchanges or custodial services
- Movement through mixing services or privacy-enhancing tools
- Conversion to stablecoins before further transfer
Each of these movements creates a decision point for the investigator. Some paths are easier to follow. Others introduce complexity that may limit what can be determined with certainty.
Need help documenting fund movement? Crypto Recovery Authority supports victims with structured evidence review and blockchain tracing guidance designed to clarify what happened and what next steps may still be worth pursuing.
Request a Confidential Case ReviewStep 4: Look for Service Exposure and Off-Ramp Points
This is often the most consequential step. Service exposure means that the traced funds appear to interact with an identifiable service — typically a centralised exchange, a payment processor, or a custodial wallet provider.
When funds reach a regulated exchange, there may be avenues for engagement. Many exchanges maintain compliance teams that cooperate with law enforcement requests and professional investigators when credible evidence is presented. This is where tracing transitions from analysis into potential action.
Off-ramp points — where crypto is converted to fiat currency — are also significant. They often involve identity verification and may represent the strongest link between the traced funds and an identifiable individual or entity.
Step 5: Build a Documented Evidence Trail
Tracing is only valuable if it is properly documented. Investigators produce structured reports that map the flow of funds, identify key addresses, note service interactions, and present the evidence in a format suitable for law enforcement, legal proceedings, or exchange compliance teams.
A well-documented tracing report typically includes:
- A visual map of the fund flow from origin to destination
- Annotated wallet addresses with transaction hashes at each step
- Identification of exchange deposits or service interactions
- Timing analysis showing when each movement occurred
- A summary of findings and assessment of what next steps may be available
Step 6: Assess What Tracing Can and Cannot Accomplish
Honest investigators are clear about the limits of their work. Tracing can reveal where funds went. It can identify patterns, clusters, and service touchpoints. It can produce evidence that supports reporting and legal action.
What tracing cannot do is guarantee recovery. Even when funds are traced to a specific exchange, recovering those assets requires cooperation from the exchange, law enforcement involvement, and often legal proceedings. These processes take time and their outcomes are never certain.
Understanding this distinction — between tracing and recovery — is one of the most important things a victim can grasp early in the process.
What Victims Should Preserve Before Data Disappears
Evidence degrades. Platforms go offline. Chat histories are deleted. The sooner victims preserve the following, the stronger the foundation for any investigative work:
- Transaction hashes for every deposit or transfer connected to the incident
- Wallet addresses — both yours and any receiving addresses you can identify
- Screenshots of the platform, dashboard, or communication with the scammer
- Records of any fees, taxes, or additional payments demanded
- Timestamps for every interaction — when you sent funds, when you noticed the issue
Request a Confidential Case Review
If you need help understanding where stolen crypto moved, what evidence should be preserved, and whether tracing may reveal meaningful next steps, Crypto Recovery Authority can help with professional case review and tracing support. Request a confidential case review to get started.
Frequently Asked Questions
Can stolen crypto really be traced?
Often, yes. Many blockchain transactions are visible and can be followed, though traceability varies by asset, movement pattern, and available evidence.
Does tracing guarantee recovery?
No. Tracing and recovery are related, but they are not the same thing. Tracing reveals where funds went — recovery depends on many additional factors.
What is service exposure?
It means the traced assets appear to interact with an identifiable service such as an exchange or custodial platform. This is often the most actionable finding in a tracing review.
What should I preserve first?
Transaction hashes, wallet addresses, screenshots, and communications connected to the transfer. The sooner you preserve this, the better.
Is tracing still useful if the funds moved quickly?
Yes. Rapid movement can still reveal patterns, routing behaviour, or service touchpoints that matter for investigation and reporting.